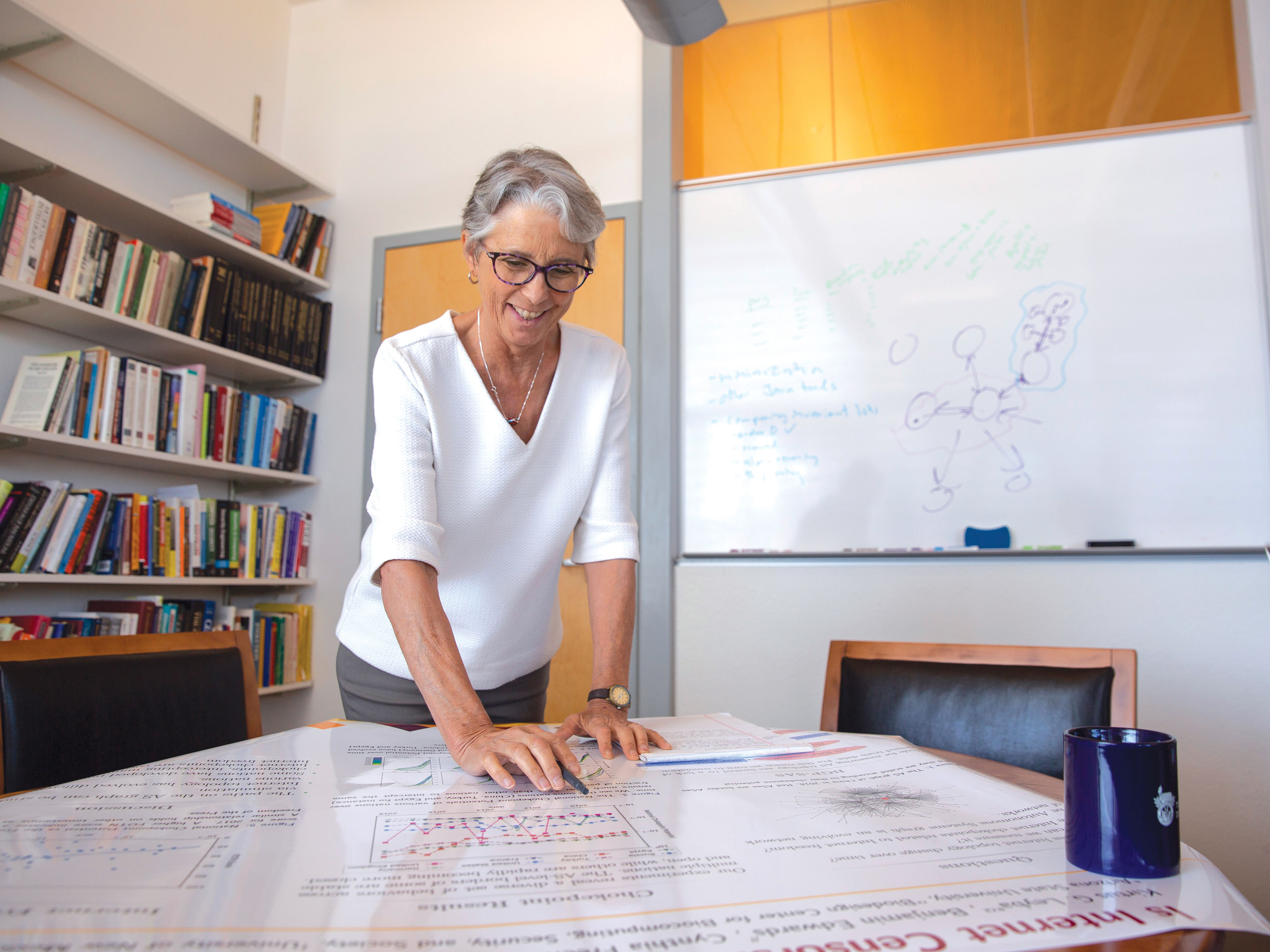
Stephanie Forrest, a professor of computer science and jointly appointed with The Biodesign Institute, studies the potential of censorship and surveillance as internet traffic crosses national borders. Photographer: Erika Gronek/ASU
Censorship and chokepoints
Protecting the free flow of information on the internet
Convergence magazine > Censorshop and chokepoints
When traveling to Beijing, you’ll likely have to take multiple flights and pass through customs to get to your destination.
If you’re searching for a Beijing hotel and visit its Chinese website, your request also travels multiple legs through internet networks, entering and exiting the territories of various countries on its way to the Chinese network hosting the website.
And like customs and border patrol, there is a potential for governments to place digital filters on information allowed to pass through borders.
The geography of the internet
The internet is a patchwork of physical networks. While it seems to operate like magic — data and communications traveling around the world at near-instantaneous speeds — internet traffic has to pass from physical network locations through physical lines to get to its destination.
We understand the real-world geography of countries and the routes across their borders very well, but we don’t have a full understanding of the routes data can take between the roughly 60,000 networks that make up the internet — or the potential for and practice of government-placed controls when that traffic crosses national borders.
Any network node internet traffic passes through when it enters or exits a country’s internal networks is called a chokepoint. These can have big implications for internet freedom and cybersecurity.
The number of potential network chokepoints in a country reflects how easily a government could tamper with internet traffic either for cybersecurity or for repressing the freedom of communication for a country’s citizens.
Stephanie Forrest’s research team is working with University of New Mexico Professor Jedidiah R. Crandall and University of California, Riverside Professor Michalis Faloutsos to develop tools and models to determine the topography of the global internet and countries’ chokepoint potential.
In a $1.4 million National Science Foundation-funded project led by Crandall to measure internet chokepoints, Forrest, a computer science professor and jointly appointed in the Biodesign Institues, is helping policymakers, cybersecurity researchers and free speech advocates address issues related to internet freedom and security by providing accurate data and analyses of chokepoints.
Wild West to “1984”
 The internet began as a borderless, global interconnected web of networks, but it has increasingly become divided along national boundaries as the internet is wielded as an instrument of power and control by governments, and as a vector of attack on our increasingly connected world of the internet of things and autonomous applications.
The internet began as a borderless, global interconnected web of networks, but it has increasingly become divided along national boundaries as the internet is wielded as an instrument of power and control by governments, and as a vector of attack on our increasingly connected world of the internet of things and autonomous applications.
“We are interested in measuring the extent to which the internet is evolving to reflect national boundaries, with relatively few border network nodes and lots of internal network nodes,” Forrest says.
While many countries are known to be restrictive about what information is allowed to pass through their networks, we lack a worldwide view of how the internet’s network structure is changing over time, especially in ways that enable censorship and surveillance.
For certain network nodes, data known as routing tables are publicly available, showing how certain nodes talk to certain other nodes. With enough data and by using simulation methods, researchers can infer a wider structure of how internet traffic is routed. But there are still gaps.
In another aspect of the NSF project, Principal Investigator Crandall is developing side channel methods for inferring which IP addresses can talk to certain other IP addresses when data about the nodes is not publicly available.
“No one else has collected data at this scale,” Forrest says. “China isn’t necessarily going to let us install programs to measure traffic and connectivity, so how do you measure what’s going on inside of China [and other places] where information is censored? It’s a technical trick to figure out a method that will let you understand what’s going on inside the country from the outside.”
Once Forrest’s team has data to fill in a more complete map of network nodes, they need the tools to map out international network structures and potential chokepoints.
“There’s an additional step of simulating where internet traffic will actually go [through the possible paths of network nodes], and we’ve created a large (1 terabyte) data set to enable this simulation. We use this dataset to quantify the chokepoint potential of any country,” Forrest says.
Forrest has studied the past decade’s shifting potential for chokepoints among countries with more and less “free” internet network architectures to those that are more restrictive, ranging from the U.S., France, Germany and the United Kingdom to China, Turkey, Egypt and Russia.
The calculated chokepoint potential over time correlates with countries’ Freedom of the Net scores — the extent to which governments restrict citizens’ rights online — and other independent measures of a country’s level of freedoms.
Models of chokepoint potential per country could also change over time correlating with events that cause countries to change their stance on how open the internet should be.
A foundation for data-driven cybersecurity policy
Seeing the chokepoint potential trends over time can provide clues for how countries may be implementing censorship, or how information is being intercepted and where. This helps internet freedom advocates create tools to help journalists avoid freedom of the press restrictions.
These models can potentially help policymakers make better decisions and understand trends in particular countries. When she worked on cyberpolicy at the U.S. Department of State, Forrest says studies like these would have been invaluable in preparing for international negotiations related to cyberpolicy.
“Our job is to develop methods for collecting the data, then collect the data and present it in a way that is even-handed and accessible to policy-makers,” says Forrest.
Currently, there’s little reliable data to assess whether a cybersecurity policy decision is likely to have its intended effect, or to see if others are following international cybersecurity agreements.
“When a tax bill comes along, economists have models in place they can run and projections they can make about likely impacts of specific proposals,” Forrest says. “We have very little ability to do that for cybersecurity, and we need large-scale data and models to do so.”
By the time the NSF project ends in 2020, Forrest’s team will make their data sets and analysis tools publicly available for anyone to use.
If you’re searching for a Beijing hotel and visit its Chinese website, your request also travels multiple legs through internet networks, entering and exiting the territories of various countries on its way to the Chinese network hosting the website.
And like customs and border patrol, there is a potential for governments to place digital filters on information allowed to pass through borders.
The geography of the internet
The internet is a patchwork of physical networks. While it seems to operate like magic — data and communications traveling around the world at near-instantaneous speeds — internet traffic has to pass from physical network locations through physical lines to get to its destination.
We understand the real-world geography of countries and the routes across their borders very well, but we don’t have a full understanding of the routes data can take between the roughly 60,000 networks that make up the internet — or the potential for and practice of government-placed controls when that traffic crosses national borders.
Any network node internet traffic passes through when it enters or exits a country’s internal networks is called a chokepoint. These can have big implications for internet freedom and cybersecurity.
The number of potential network chokepoints in a country reflects how easily a government could tamper with internet traffic either for cybersecurity or for repressing the freedom of communication for a country’s citizens.
Stephanie Forrest’s research team is working with University of New Mexico Professor Jedidiah R. Crandall and University of California, Riverside Professor Michalis Faloutsos to develop tools and models to determine the topography of the global internet and countries’ chokepoint potential.
In a $1.4 million National Science Foundation-funded project led by Crandall to measure internet chokepoints, Forrest, a computer science professor and jointly appointed in the Biodesign Institues, is helping policymakers, cybersecurity researchers and free speech advocates address issues related to internet freedom and security by providing accurate data and analyses of chokepoints.
Wild West to “1984”
The internet began as a borderless, global interconnected web of networks, but it has increasingly become divided along national boundaries as the internet is wielded as an instrument of power and control by governments, and as a vector of attack on our increasingly connected world of the internet of things and autonomous applications.
“We are interested in measuring the extent to which the internet is evolving to reflect national boundaries, with relatively few border network nodes and lots of internal network nodes,” Forrest says.
While many countries are known to be restrictive about what information is allowed to pass through their networks, we lack a worldwide view of how the internet’s network structure is changing over time, especially in ways that enable censorship and surveillance.
For certain network nodes, data known as routing tables are publicly available, showing how certain nodes talk to certain other nodes. With enough data and by using simulation methods, researchers can infer a wider structure of how internet traffic is routed. But there are still gaps.
In another aspect of the NSF project, Principal Investigator Crandall is developing side channel methods for inferring which IP addresses can talk to certain other IP addresses when data about the nodes is not publicly available.
“No one else has collected data at this scale,” Forrest says. “China isn’t necessarily going to let us install programs to measure traffic and connectivity, so how do you measure what’s going on inside of China [and other places] where information is censored? It’s a technical trick to figure out a method that will let you understand what’s going on inside the country from the outside.”
Once Forrest’s team has data to fill in a more complete map of network nodes, they need the tools to map out international network structures and potential chokepoints.
“There’s an additional step of simulating where internet traffic will actually go [through the possible paths of network nodes], and we’ve created a large (1 terabyte) data set to enable this simulation. We use this dataset to quantify the chokepoint potential of any country,” Forrest says.
Forrest has studied the past decade’s shifting potential for chokepoints among countries with more and less “free” internet network architectures to those that are more restrictive, ranging from the U.S., France, Germany and the United Kingdom to China, Turkey, Egypt and Russia.
The calculated chokepoint potential over time correlates with countries’ Freedom of the Net scores — the extent to which governments restrict citizens’ rights online — and other independent measures of a country’s level of freedoms.
Models of chokepoint potential per country could also change over time correlating with events that cause countries to change their stance on how open the internet should be.
A foundation for data-driven cybersecurity policy
Seeing the chokepoint potential trends over time can provide clues for how countries may be implementing censorship, or how information is being intercepted and where. This helps internet freedom advocates create tools to help journalists avoid freedom of the press restrictions.
These models can potentially help policymakers make better decisions and understand trends in particular countries. When she worked on cyberpolicy at the U.S. Department of State, Forrest says studies like these would have been invaluable in preparing for international negotiations related to cyberpolicy.
“Our job is to develop methods for collecting the data, then collect the data and present it in a way that is even-handed and accessible to policy-makers,” says Forrest.
Currently, there’s little reliable data to assess whether a cybersecurity policy decision is likely to have its intended effect, or to see if others are following international cybersecurity agreements.
“When a tax bill comes along, economists have models in place they can run and projections they can make about likely impacts of specific proposals,” Forrest says. “We have very little ability to do that for cybersecurity, and we need large-scale data and models to do so.”
By the time the NSF project ends in 2020, Forrest’s team will make their data sets and analysis tools publicly available for anyone to use.